|
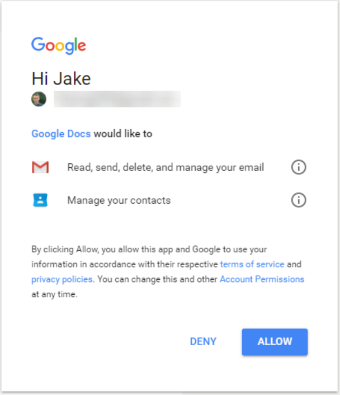
Ransomware attacks have been in the headlines a lot of late. Did you know that 65% of all ransomware attacks happen through phishing emails? Therefore, email security needs to be a major focus when delivering security awareness training. It is likely that future variants of the recent WannaCry ransomware attack will be delivered via phishing emails. As reported earlier this month, some Gmail users fell victim to a massive phishing attack that frightened many… a phishing attack that targets all your contacts. Now let us look at how gmail users were susceptible to the phishing attack. THE PHISHING EMAIL Gmail users received an email (from a known sender) that was an invitation to view a shared Google Doc. After clicking the link in the invitation email, users were directed to a legitimate “Google – Choose An Account” screen, after which they were prompted to authorize Google Doc to access their Gmail account. Simply click “Allow”… With no login prompt… Sound suspicious yet? THE HACKAt this point, it was not Google Docs requesting access – but actually a malicious app. As Reddit carefully detailed, this hack would actually:
THE PROTECTIONSonicWall™ Email Security now integrates with the Capture Advance Threat Protection service, to deliver fine-grained and user-transparent inspection of SMTP-based traffic. The cloud-based Capture ATP service can scan a broad range of email attachment types, analyze them in a multi-engine sandbox, and block dangerous files or emails before they reach your network. SonicWall Email Security with Capture ATP gives you a highly effective and responsive defense against email-borne threats, including ransomware, phishing, spoofing, spam and viruses. WHAT ELSE YOU CAN DOTo avoid phishing scams, below is a refresher on what you can do to not fall prey:
Download Solutions Brief: What your next-gen email security needs to stop advanced threats. Kaizen365 Technology is a Sonicwall partner in Jordan which can help you to achieve all the above and more by our professional team who is certified and qualified to help you.
0 Comments
Your comment will be posted after it is approved.
Leave a Reply. |
AuthorKaizen365 Technology. ArchivesCategories
|

 RSS Feed
RSS Feed